The very first EEAS FIMI report gives us valuable information about the tactics, techniques, and procedures that Russia and China use to manipulate information domain and their audiences.
The very first EEAS Report on Foreign Information Manipulation and Interference (FIMI) Threats was published today and can now be downloaded in full here. The report sets up a common framework for countering foreign threat actors. It also provides us with a number of juicy details on threat actor behaviour.
Table of Contents
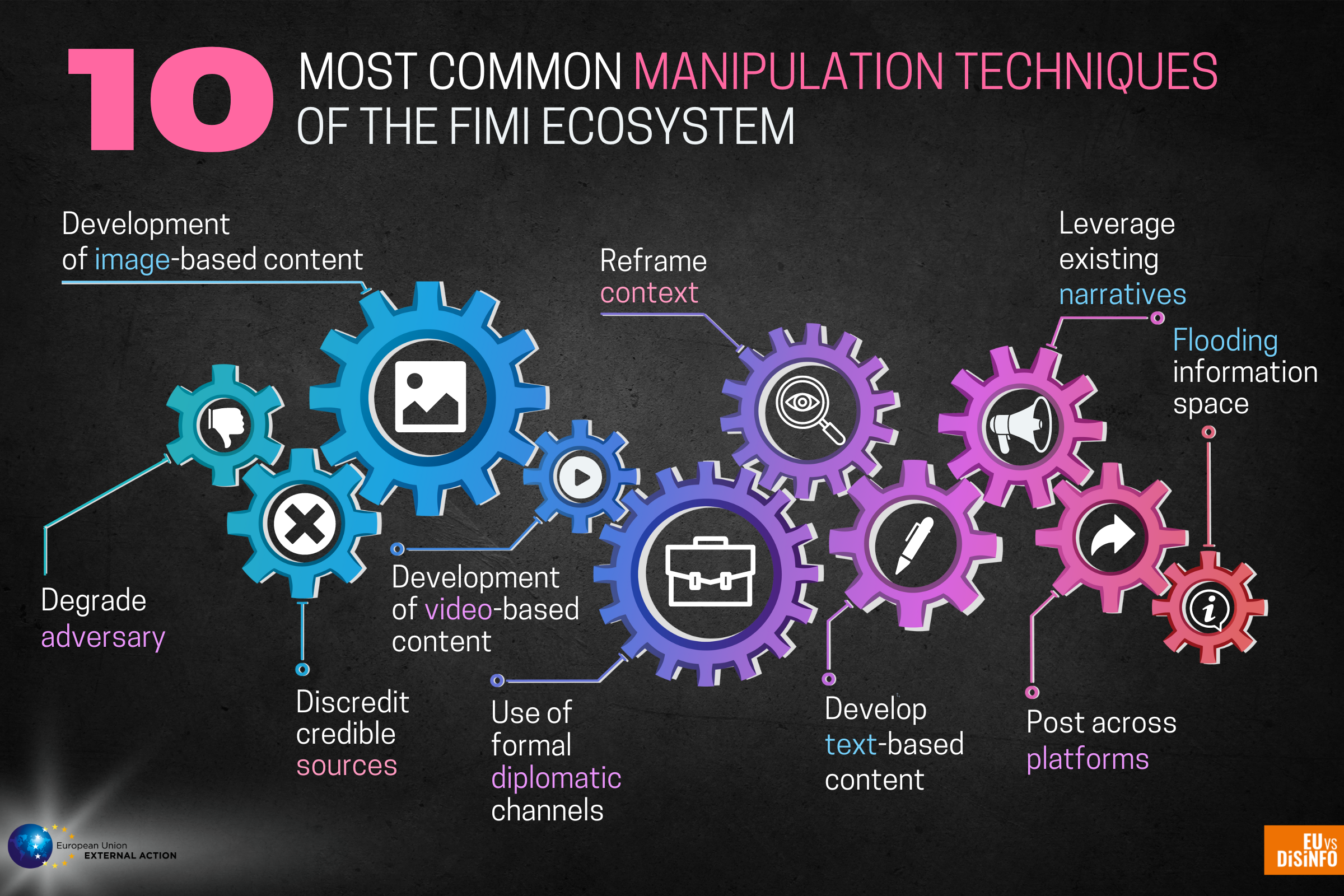
In this piece, we concentrate on the pro-Kremlin ecosystem and list some of the most common manipulative techniques, tactics, and procedures (TTPs) identified in the report.
Some key findings
Russia’s unprovoked and unjustified full-scale invasion of Ukraine dominates the Report’s data sample. Other identified key themes include increasing Russian influence, attacking public officials, hyping the energy crisis, and pushing conspiracy theories about biological and nuclear weapons. All these themes have been featured a number of times in our articles and disinfo database.
With 60 cases linked with the Russian invasion of Ukraine, the main driver of these information manipulations was supporting the invasion. The aim was and remains to distract target audiences, deflect blame, or to direct the audience’s attention to something completely different. For example, pro-Kremlin outlets often degraded adversaries or deployed whataboutisms.

The Threat Report also establishes that disinformation and other information manipulations rarely appear in only one language. In the analysed sample data set, at least 30 languages were used, including 16 EU languages. In the case of the pro-Kremlin ecosystem, Russian and English were the most used languages in the sample data set.
For example, we have witnessed a multilingual approach in manipulating the information space regarding energy security. Audiences across Europe have been targeted in their native tongues, including German, French, and Spanish.
The sample data set also indicates that there is some cooperation between Russian and Chinese information manipulation efforts. In one example, manipulation in a Chinese ecosystem, amplified by Chinese diplomatic accounts and state-controlled channels, travelled to the Russian ecosystem for reuse and redistribution.
The opposite has happened as well, as when Chinese state-controlled outlets and diplomats amplified material originating from the Russian information manipulation ecosystem.
The most common manipulation techniques
According to the sample data, images and videos are typically used to manipulate information and spread disinformation. Additionally, to maximise the exposure and impact, manipulative content would often be propagated by cross-posting it across platforms, communities, and groups.
Russian diplomatic channels spread and amplify disinformation and are an important part of the ecosystem. In June 2022, one such Russian channel spread disinformation regarding food security. EUvsDisinfo quickly debunked it.
Threat actors also use a combination of different techniques and tactics. For example, official diplomatic accounts have been used to attack and degrade credible sources or adversaries. Often threat actors employ image and video content, including fabricated material, to support such attacks. One recent example that we have reported on includes a pro-Kremlin attack against the European Union Military Assistance Mission (EUMAM).
A featured technique in the report is the impersonation of legitimate and trusted entities. Russian threat actors have impersonated legitimate media outlets such as satirical magazines, international media outlets, and European institutions and politicians.
The motive behind such impersonation is to steal the legitimacy and authority of the impersonated entity to manipulate audiences trusting the impersonated entities. For example, pro-Kremlin disinformation spreaders used such stolen legitimacy to attack Ukraine and Ukrainian President Volodymyr Zelenskyy last year.
Countering both malicious narratives and behaviour
The report gives us valuable information about the tactics, techniques, and procedures that Russia and China use to manipulate the information domain.
These findings will further support and guide the counter-disinformation and information manipulation efforts globally. Understanding manipulative behaviour goes hand-in-glove with exposing and uprooting the deceitful narratives and FIMI ecosystems that Russia and other actors use to conduct their malicious activities.
Download the full report and delve deeper into the dark arts of hostile actors trying to manipulate and poison our information environment and minds.







